Lesson 3 (Beta)
Social Engineering: The Oldest Hack
About This Lesson:
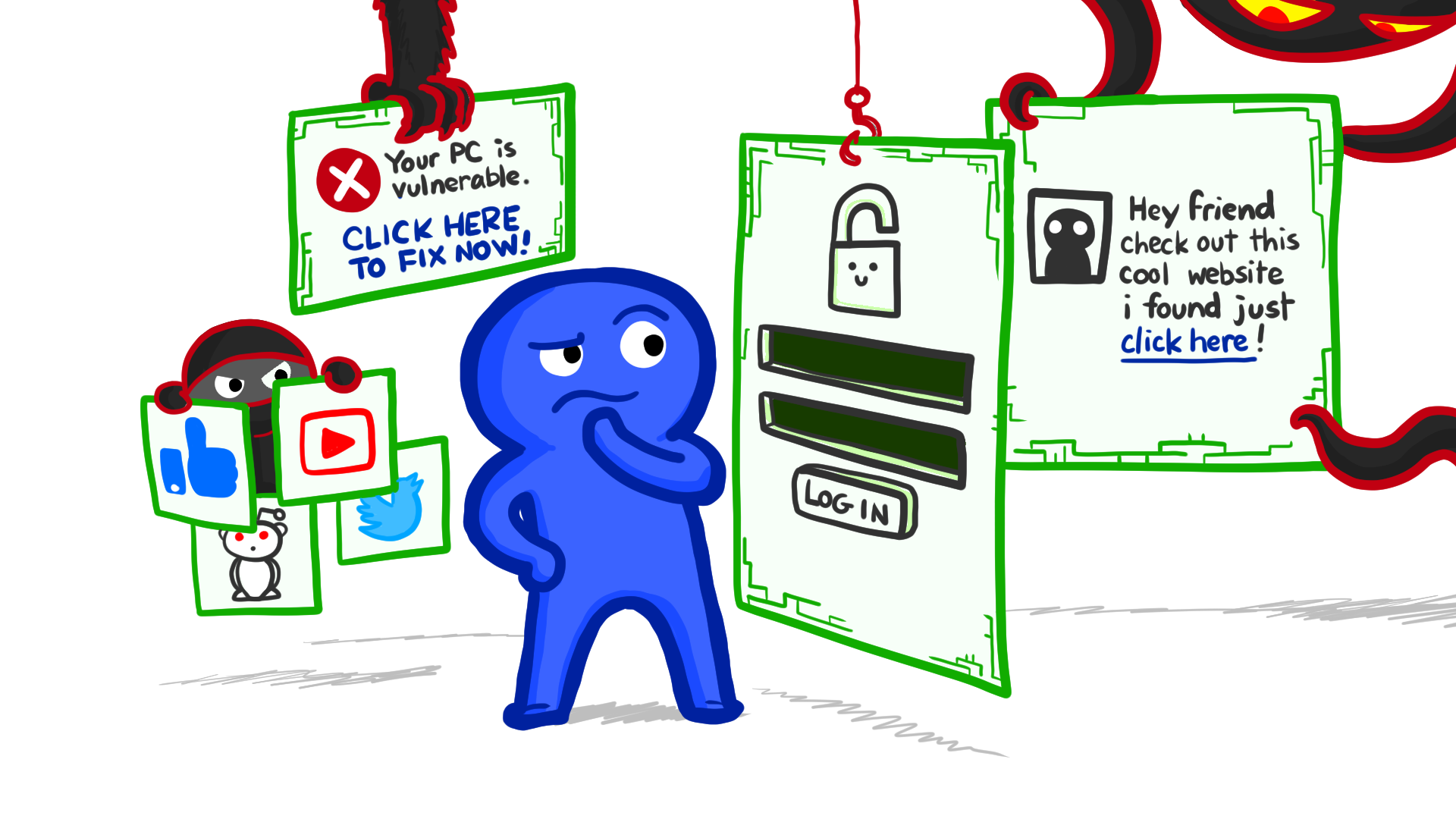
Lesson 3 explores the human side of cybersecurity: how social engineering attacks work and why they’re important to a good threat model.
Intended Audience: High school students or early undergraduates. Geared towards AP Computer Science Principles, but compatible with any introductory computer science course.
Delivery Format: Traditional classroom.
Duration for Whole Lesson: 75 minutes (with options to shorten or lengthen).
Lesson Rationale
Online scams have a lot in common with classic scams. They both take advantage of the same human weaknesses. Usually they involve some combination of pretending to be a different person, delivering false information, and playing on the target’s emotional responses to trick them into doing something they shouldn’t do or wouldn’t normally do.
This lesson encourages students to think about how we verify identity and truthfulness over different communication channels — to the extent that we verify anything at all — and how those different verification processes can be manipulated by someone who wants to run a scam.
Learning Objectives
After completing this lesson:
- Students can explain why social engineering is an important consideration for cybersecurity.
- Students can analyze how particular social engineering attacks take advantage of specific features of the Internet and of human nature.
- Students can discuss the limitations of visual inspection for preventing phishing attacks.
- Students can compare similarities and differences between offline and online scams.
- Students can enumerate some strategies for personally avoiding scams.
Alignment with AP Computer Science Principles -- SY 2020--21 Onward
This lesson addresses standards laid out in the AP Computer Science Principles Framework for 2020–21, Fall 2019 version.
Supports the following Learning Objectives under Big Idea 5, Impact of Computing:
LO IOC-1.A Explain how an effect of a computing innovation can be both beneficial and harmful.
LO IOC-1.B Explain how a computing innovation can have an impact beyond its intended purpose. Essential Knowledge points covered:
- EK IOC-1.B.1 Computing innovations can be used in ways that their creators had not originally intended.
LO IOC-2.A Describe the risks to privacy from collecting and storing personal data on a computer system. Essential Knowledge points covered:
- EK IOC-2.A.12 PII can be used to stalk or steal the identity of a person or to aid in the planning of other criminal acts.
LO IOC-2.B Explain how computing resources can be protected and can be misused.
LO IOC-2.C Explain how unauthorized access to computing resources is gained. Essential Knowledge points covered:
- EK IOC-2.C.1 Phishing is a technique that attempts to trick a user into providing personal information. That personal information can then be used to access sensitive online resources, such as bank accounts and emails.
- EK IOC-2.C.5 A malicious link can be disguised on a web page or in an email message.
- EK IOC-2.C.6 Unsolicited emails, attachments, links, and forms in emails can be used to compromise the security of a computing system. These can come from unknown senders or from known senders whose security has been compromised.
LO IOC-1.F Explain how the use of computing can raise legal and ethical concerns.
Also touches on the following Essential Knowledge:
Under Big Idea 5, Impact of Computing:
- EK IOC-1.A.1 People create computing innovations.
- EK IOC-1.A.2 The way people complete tasks often changes to incorporate new computing innovations.
- EK IOC-1.A.3 Not every effect of a computing innovation is anticipated in advance.
- EK IOC-1.A.4 A single effect can be viewed as both beneficial and harmful by different people, or even by the same person.
- EK IOC-1.B.2 Some of the ways computing innovations can be used may have a harmful impact on society, economy, or culture.
- EK IOC-1.F.8 As with any technology or medium, using computing to harm individuals or groups of people raises legal and ethical concerns.
- EK IOC-1.F.11 Computing innovations can raise legal and ethical concerns.
- EK IOC-2.A.1 Personally identifiable information (PII) is information about an individual that identifies, links, relates, or describes them.
- EK IOC-2.A.5 Technology enables the collection, use, and exploitation of information about, by, and for individuals, groups, and institutions.
- EK IOC-2.A.11 Information placed online can be used in ways that were not intended and that may have a harmful impact. For example, an email message may be forwarded, tweets can be retweeted, and social media posts can be viewed by potential employers.
- EK IOC-2.A.15 Information posted to social media services can be used by others. Combining information posted on social media and other sources can be used to deduce private information about you.
- EK IOC-2.B.1 Authentication measures protect devices and information from unauthorized access. Examples of authentication measures include strong passwords and multifactor authentication.
- EK IOC-2.B.10 All real-world systems have errors or design flaws that can be exploited to compromise them. Regular software updates help fix errors that could compromise a computing system.
Provides opportunities to use the following Computational Thinking Practices:
P5 Computing Innovations: Investigate computing innovations.
- P5.C Describe the impact of a computing innovation.
- P5.D Describe the impact of gathering data.
- P5.E Evaluate the use of computing based on legal and ethical factors.
P6 Responsible Computing: Contribute to an inclusive, safe, collaborative, and ethical computing culture.
- P6.A Collaborate in the development of solutions.
- P6.B Use safe and secure methods when using computing devices.
Cybersecurity Ethics Agreement
Some activities in this lesson involve learning skills that could be used to attack networked systems. Before beginning your cybersecurity unit, we recommend you ask students to sign an agreement such as the one below. The agreement commits them to use their powers only for good, and lays out some specifics of what that means.
Download Agreement: "Cybersecurity Ethics Agreement"
Be sure to give students plenty of time to read through the agreement (emphasize that this isn't a click-through yeah-sure-whatever terms of service agreement!) and invite them to ask questions if anything is unclear. Give them a copy to sign and a copy to keep.
- Check your district's policies to see whether students will need to have their parents sign the agreement as well.
Credits: Inspiration for the points to cover in this agreement came from Avi Rubin, Michael E. Whitman and Herbert J. Mattord (the Hands-On Information Security Lab Manual), an anonymous CS teacher from a Facebook group, and EC-Council’s Code of Ethics.
“Engage” Activities:
Introduce the topic, probe prior knowledge, and ignite students’ interest. (Choose one Engage activity, or use more if you have time.)
Quick Thought Exercise: Voice vs. Text
Estimated Time: 5-15 minutes.
What You’ll Need: Blackboard/whiteboard (optional).
Description: This quick class discussion gets students thinking about how we verify someone’s identity over commonly used communication channels.
Determining identity can seem very simple — but at the same time, it can be quite difficult. Sometimes you “just know” and sometimes you have to use all available information to rule out other possibilities. Many scams rely on convincing the target to do something by pretending to be someone they trust or an authority figure.
Ask: When a friend calls you, how do you know the voice on the phone is the person they claim to be?
Possible Answers Include:
- Caller ID.
- The content. Is that the kind of thing they would say? The kind of topics they’d usually talk about?
- Their voice, tone, mannerisms, whether it’s a typical time of day for them to call…
Ask: What about when a friend texts you? How do you know the text was sent by the person you think it’s from?
Possible Answers Include:
- Caller ID.
- The content of the text.
- Context, time of day…
Ask: How is it different identifying a person who calls on the phone vs. identifying a person who sent a text?
Possible Answers Include:
- Voices are pretty unique and require some effort to fake.
- A lot of individual quirks of speaking style are flattened in text (no intonation, no rhythm, fewer filler words).
- Over text, it’s harder to tell if someone is hesitating before responding to something they should be able to answer without thought.
Extended Version: Additional Questions
Ask: What would you do if you weren’t sure the person was who they said they were?
Possible Answers Include:
- You can ask a question that only they would know the answer to.
- You can ask them to take a specific action on another medium that only they should be able to do. (For example, “If this is really you, then go to my Instagram and like the photo of us from last week.”)
- If they texted, you can ask them to call you.
Ask: Are the ways of recognizing someone or verifying identity that we’ve talked about foolproof? How could they be manipulated?
Possible Answers Include:
- Caller ID can be spoofed, for both voice calls and texts.
- It’s easier to trick someone if you know the person you’re trying to impersonate. Even if you don’t, it can be easy to find basic information, especially information shared on social media, and use it to fake your way through answering simple questions that are used to prove identity.
- On the phone, it’s easier to notice if something’s off with how someone talks. But if you have no reason to feel skeptical, it wouldn’t necessarily occur to you there was something shady going on. (For example, you might assume anything unusual is due to a bad connection or a weird mood.)
Media Resource: "What Happens When You Dare Expert Hackers to Hack You"
Estimated Time: 3-10 minutes.
What You’ll Need: Computer, projector, and speakers.
Video Summary: A social engineering expert demonstrates how she can get access to a journalist’s cell phone account over the phone (vishing), manipulating the customer service agent’s attention with distractions and appeals to urgency.
Video: What Happens When You Dare Expert Hackers to Hack You
- Excerpt with brief explanation of social engineering, then vishing demo (end at 00:04:04 for a 2m39s clip)
- Excerpt with vishing demo only (end at 00:04:04 for a 2m5s clip)
- Content Advisory: Video is preceded by ads with unpredictable content. In the video, the journalist uses a swearword.
Produced by Fusion Media as part of their “Real Future” series.
Optional Extension
Follow up with one or a few of the following questions:
- Why would someone do this? What could they do with the information?
- What potential consequences can you think of for the person who got hacked?
- What exactly is the “hack” here?
- What technical knowledge or tools did the hacker use?
- Note: It goes by quickly, but the hacker uses a tool to spoof the number she’s calling from.
- What non-technical knowledge and skills did the hacker use?
- What did she do to reduce the customer service agent’s likelihood of being cautious? Their ability to think clearly?
- How did she make use of social norms and/or stereotypes?
- Would different methods have worked better for someone else? For example, if she were a man, what might she have tried?
- Note: If you’re planning to ask this question, it may be a good idea to remind students at the beginning of the exercise about ground rules for respectful classroom discussion.
- What technical knowledge or tools did the hacker use?
- Can you think of any security measures or procedures that could have prevented this hack from succeeding? What would you advise Verizon to do?
Computing in the News - Cybersecurity Edition
View Outline: “Computing in the News – Cybersecurity Edition”
Coming Soon: Specific questions and example articles for Lesson 3, without having to go off-page.
“Explore” Activities:
Ground students’ learning in firsthand experience and spark new ideas.
Small-Group or Individual Activity: Real or Phish?
Estimated Time: 15-20 minutes
What You’ll Need: Copies of the “Real or Phish?” worksheet
Description: Students examine phishing as an example of an common online scam. Phishing takes advantage of human weaknesses and the fact that websites use passwords for authentication.
Students will get practice inspecting emails and talking about what would make an email suspicious. The activity is intentionally unplugged, but the worksheet asks how students would inspect each email if they were on a computer or phone (e.g. hovering over the link or right-clicking the button to check the link destination, or doing a search to get more information about the sender or the company named in the email).
Download Worksheet: “Real or Phish?”
Running the Activity:
- Pass out worksheets and give students time to read through the instructions.
- Break students into small groups, if relevant (or use as an individual activity).
- Have students inspect the emails on the worksheet and decide whether they are real or a phishing attempt. They then fill out the questions for each email.
- Bring the class back together. For each email, ask a group or student to share their answer for “real or phish?” then ask them to describe how they chose their answer. Engage the class in a discussion of each email using these prompts:
- What did you look for?
- Which one was the most difficult to tell? Why?
- Which one was easiest to tell? Why?
- What do you do when you see a suspicious email or message?
- How confident are you in your ability to spot a phishing email?
- Try to cover these points in the discussion:
- The activity is meant to feel difficult and ambiguous.
- It is difficult, if not impossible, to tell whether an email is a phishing attack by visual inspection alone.
- There are some tells for a scam email, but they aren’t foolproof. Legitimate emails still break the “rules” sometimes.
- Context is the most important thing. If you get an email from a bank that’s not yours, you know that it’s not for you. If you get an email about an activity, purchase, or transaction that you can’t remember, you should probably ignore it.
- If you get an email demanding you take immediate action, you should go directly to the site or the app and investigate your account details.
- Later in the lesson, we’ll talk more about the reasons why phishing works and how to avoid falling victim to a scam.
Worksheet answer key and some possible answers for the free-answer questions (reasoning and additional inspection methods):
- USPS notification: Phish
- The From address has a random-sounding domain; it’s not usps.com.
- The subject is “Information”, which is much less specific than you’d expect from a government agency with a reputation for being precise.
- The language is awkward — especially unusual for a form notice from a government agency. A “shipping label” is what the sender puts on the package, not what the recipient uses to claim it.
- Your email program tagged it with a little red flag at the top.
- What link does the button show if you hover over it?
- UC Berkeley library account: Phish
- Do you attend UC Berkeley? Do you have a UC Berkeley library account? Receiving a phishing email for an account you don’t have is an easy way to identify a scam.
- If you had an account, how likely would it be that it would suddenly expire due to inactivity? Is it likely that a university library would require students and staff to log in frequently to maintain an account, or would they keep the account active as long as the person was associated with the university?
- Did the university tell you anything about account expiration when they gave you the account?
- If you could see the From address, you could check whether it was in the berkeley.edu domain.
- What do the reactivation and email-for-help links look like if you hover over them? Do they match the text you see?
- If you had a UC Berkeley library account but you really weren’t sure if the email was legit, you could type the URL directly into the URL bar, and check your password settings from there.
- BestBuy order: Phish
- The From address has a random-sounding domain; it’s not bestbuy.com.
- The email is addressed to “dave” but the email says “Sir/Madam.” Most, though not all, real emails are addressed using your name.
- It’s suspicious to ask you to fill out a separate form to correct the address.
- The language is awkward, especially the message about timing.
- It threatens you with deducting $17 from your refund, which is a random amount and doesn’t seem likely for Best Buy to do.
- Did you even order anything from Best Buy recently?
- On the other hand: The boilerplate parts of the message, like the footer, seem very standard for an online retailer.
- Zoom password: Real
- Do you have a Zoom account?
- If you have an account, did you just request to change your password?
- Sent from an email address in the zoom.us domain, which matches the name of the service it claims to be from. But .us is a slightly unusual top-level domain for a big service company; how do you know that it shouldn’t be zoom.com?
- If you click on the dropdown next to the To line to get the full header, is the Reply-To address also in the zoom.us domain?
- The body of the message includes the recipient’s real name.
- What do the links look like if you hover over them?
- Bank payment: Phish
- Have you ever used a service called “epayment.com” to receive money? Do you know whether your bank is associated with such a company?
- Are you expecting someone to wire money to you?
- The name in the From address says “Bank” instead of the name of a bank.
- The Reply-To address is a Gmail account (which would be unusual for a bank), and it doesn’t match the From address domain.
- The language is awkward.
- You shouldn’t open zip files from unexpected senders.
Image Credits for “Real or Phish?”:
- USPS notification: Screenshot by David Ellis for Security Metrics. (Copyright phishy author.)
- UC Berkeley library account: Screenshot by Teaching Security from the Berkeley Information Security Office’s phishing email collection. (Copyright phishy author.)
- BestBuy order: Screenshot by David Ellis for Security Metrics. (Copyright phishy author.)
- Zoom password: Screenshot by Teaching Security. Email text copyright Zoom.us.
- Bank payment: Screenshot by David Ellis for Security Metrics. (Copyright phishy author.)
Alternative Exercise
The activity “Something’s Phishy” from our sister project Teaching Privacy has a similar structure, but includes mouseover pop-ups rather than leaving further inspection as an open topic for discussion.
Small-Group or Whole-Class Media Discussion: "Obvious Scams"
Estimated Time: 7-15 minutes.
What You’ll Need:
- Small-group version: Student computers with sound (one per group).
- Whole-class version: Computer, projector, and speakers.
Description: Students watch excerpts from a YouTube video highlighting ten common scams, to get them talking about scams and why people fall for them.
Video: Obvious Frauds People Actually Fell For
- 10. Nigerian Prince/419 Scam
- 9. Craigslist Scams/Fraudulent Sellers & Buyers
- 8. Get Rich Quick Schemes/Pyramid Schemes & MLMs
- 7. Phishing & Identity Theft
- 6. Senior Fraud/Scamming the Elderly
- 5. Tourist Scams
- 4. Modeling Scams/Fraudulent Agencies
- 3. Wire Transfer Scams
- 2. Money Investment Scams/Ponzi Schemes
- 1. Religious Scams & Fake Charities
- Content Advisories: “Modeling Scams” includes mention of sex trafficking scams. There is a meme in “Nigerian Prince Scam” (using a photo of a Zulu king) and a comment about churches in “Religious Scams” that some students may find disrespectful. (In addition, video is preceded by ads with unpredictable content.)
Produced by TopTenz.
Options
- Put the students in small groups to each watch a segment of the video, discuss, and report back to the class on the questions.
- Watch a couple of the video segments all together, and discuss the questions for each as a class. (All of the scams discussed can use the Internet and often do, but the most obviously Internet-enabled are numbers 10-7.)
Discussion Questions
For each scam, ask:
- What’s the point of the scam? What is the attacker trying to gain?
- Who is being scammed?
- What are the potential consequences for the person being scammed?
- Why does the scam work?
- What suggestions are given for how a potential victim could avoid the scam?
- Are there any other suggestions that you would make?
“Explain” Activities:
Introduce important facts and underlying concepts.
Slide Deck: Social Engineering and Online Scams
Estimated Time: 10-30 minutes.
What You’ll Need: Computer, projector, and speakers.
Description: In this presentation, students consider why scammers scam, learn about general techniques for influencing people are used in online social engineering attacks, and discuss differences between online and offline scams.
Access Slide Deck: “Social Engineering and Online Scams”
Contents:
- Defines social engineering and prompts students to think about motives, slides 2–4
- Introduces the question of how scams take advantage of human nature, slide 5
- Summarizes Cialdini’s principles of influence, slides 6–12
- Invites students to think about how those principles are used, slides 13–14
- Discusses how scams take advantage of the nature of the Internet, slides 15–20
- Introduces approaches to self-protection, slide 21
- “Identity Isn’t Guaranteed” video from our sister project Teaching Privacy, slide 22
Coming Soon: Graphic organizer for student note-taking.
Additional Background for Teachers
Cialdini’s Principles of Influence:
- Cialdini’s website. Includes an explainer video and lengthy explanations, with updated terminology. Aimed at marketers. https://www.influenceatwork.com/principles-of-persuasion/
- Synopsis on Medium.com. Shortish, user-friendly explanations, aimed a general audience. https://medium.com/@alyjuma/the-6-principles-of-influence-how-to-master-persuasion-2f8c581da38b
Protecting Yourself from Scams:
- Background and extensive advice from the Australian Competition & Consumer Commission: https://www.scamwatch.gov.au/get-help/protect-yourself-from-scams
- Tips from the U.S. Federal Trade Commission: https://www.consumer.ftc.gov/articles/0060-10-things-you-can-do-avoid-fraud
Video: "Identity Isn't Guaranteed"
Estimated Time: 8 minutes.
What You’ll Need: Computer, speakers, and projector.
Description: “Identity Isn’t Guaranteed” delves into why we have such a hard time knowing who to trust on the Internet, what can happen to our private information if we trust the wrong person (or bot), and how to protect ourselves against being fooled. Humorous illustrations by Ketrina Yim turn each point into a memorable story.
Produced by our sister project, Teaching Privacy. Includes human-generated closed captions.
Also included in the slide deck for this lesson.
“Elaborate” Activities:
Go deeper into the underlying concepts and/or let students practice important cybersecurity skills. (Choose one Elaborate activity, or use more if you have time.)
Small-Group Activity: Analog to Digital
Estimated Time: 25-30 minutes
What You’ll Need:
- Copies of the “Analog to Digital” assignment handout (includes a list of classic scams) — one copy per student
- The summary of Cialdini’s principles of influence from ReadingGraphics — you will need either:
- One paper copy per student, or
- A computer, projector, and screen to project it
- Materials for making a poster:
- Giant sticky notes, flip chart/easel pads, butcher paper, or poster board — one per group
- Markers
Description: What’s old is new again in the scam world with the Internet! In this activity, students look at classic analog scams and explain how those scams could play out in the digital world.
Using questions and scam descriptions from a worksheet, each group creates a quick poster for their chosen or assigned scam (20 minutes). Then the class can do a walk-the-wall exercise to share results (5–10 minutes).
Download Handout: “Analog to Digital”
Download Example Answers: “Analog to Digital: Sample Responses” (Since this is a relatively constrained activity, we recommend that, if you wish to share an example with students, you pick one and eliminate it as a possible group choice.)
“Evaluate” Activities:
Assess students’ understanding of the material and development of new skills.
Assignment: Sketch a Sketchy Scheme
Estimated Time: 45-60 minutes.
What You’ll Need:
- Copies of the “Sketch a Scheme” assignment handout
- The summary of Cialdini’s principles of influence from ReadingGraphics — you will need either:
- One paper copy per student, or
- A computer, projector, and screen to project it
- Student computers to write up answers, or pens and paper
Description: Students (individuals or groups) come up with a new digital confidence trick, and a plan for how they would implement it.
Download Assignment Handout: “Sketch a Scheme”
Optional Extensions
- Students try out their trick on students in a different classroom or on the whole school (with permission, of course).
- Add a question to the assignment: “Is there anything someone could do to protect themself against this type of scam?”
Download Example: “Sketch a Scheme (Sample Response)”
More for Teachers
Resources and background information to help you brush up on the technical nitty-gritty and be prepared for student questions.
